What are the Methods and Motives for Hacking? - VMware Security Blog - VMware


Hackathon @ VMware Explore 2023: The projects! - VMware {code}

A Complete Guide to Easy VMWare Patch Management

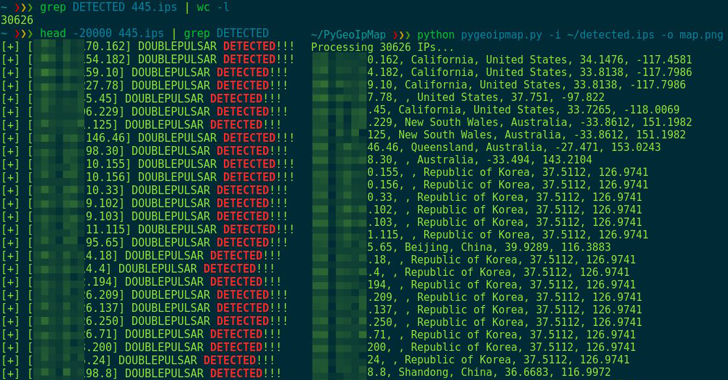
Security Snacks #20 - How to get hacked with Nginx or VMWare

How to Create a Virtual Hacking Lab: The Ultimate Hacker Setup

VMware Authentication Bypass Vulnerability (CVE-2022-22972

How to secure your VMware ESXi hosts against ransomware - Truesec

ESXiArgs Ransomware Targets VMware Vulnerability
TuxCare Blog - Insights and News on Linux Technology
CVE-2022-22948: Sensitive information disclosure in VMware vCenter

Secure Your VMware ESXi Hosts

Urgent: VMware Warns of Unpatched Critical Cloud Director

)