Chapter 10 Vendor: STM32 Embedded Systems Security and TrustZone
A free ebook on Embedded systems security, TrustZone, and reverse engineering firmware.
Chapter 10 Vendor: STM32 Embedded Systems Security and TrustZone
Sustainability, Free Full-Text

PDF] Demystifying Arm TrustZone
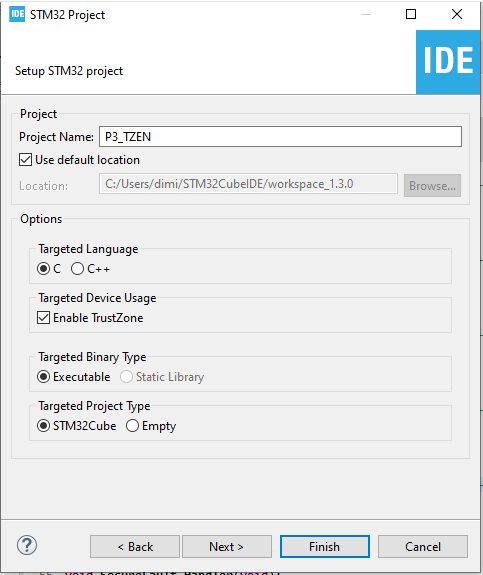
Chapter 10 Vendor: STM32 Embedded Systems Security and TrustZone
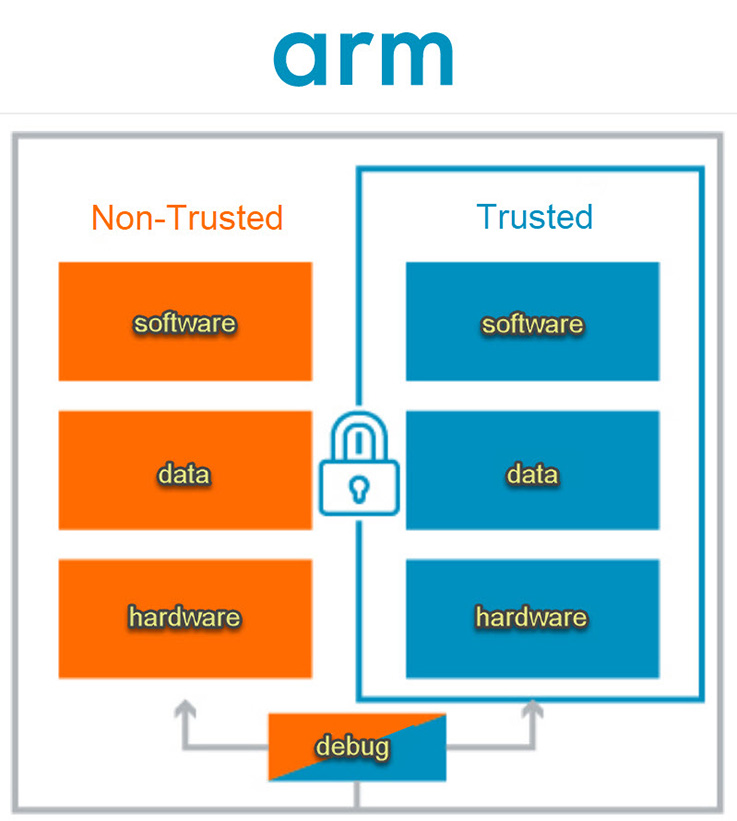
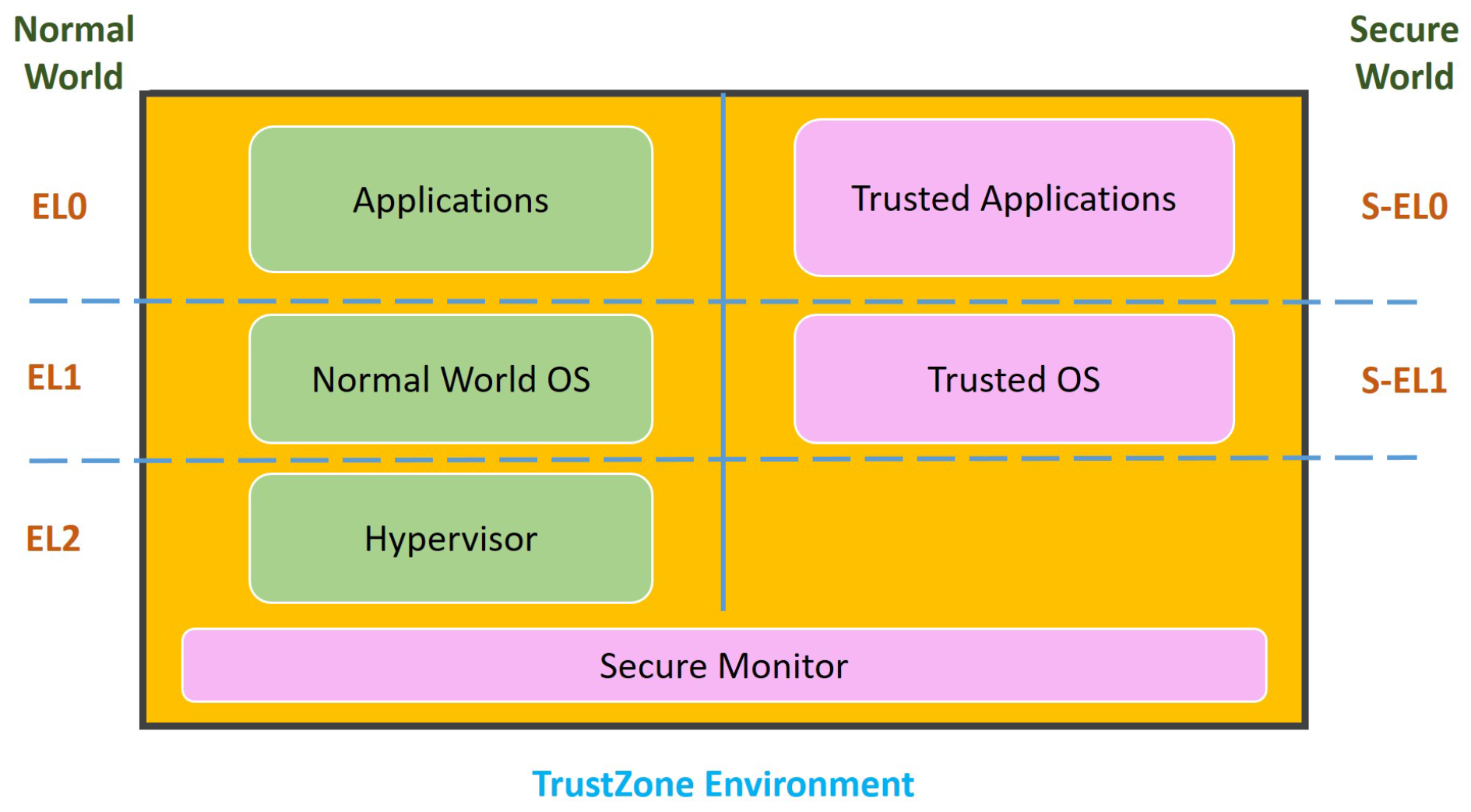
Arm TrustZone explained

PDF) On Security of TrustZone-M Based IoT Systems

PDF) On Security of TrustZone-M Based IoT Systems

Chapter 4 Basics: TrustZone-M Embedded Systems Security and TrustZone
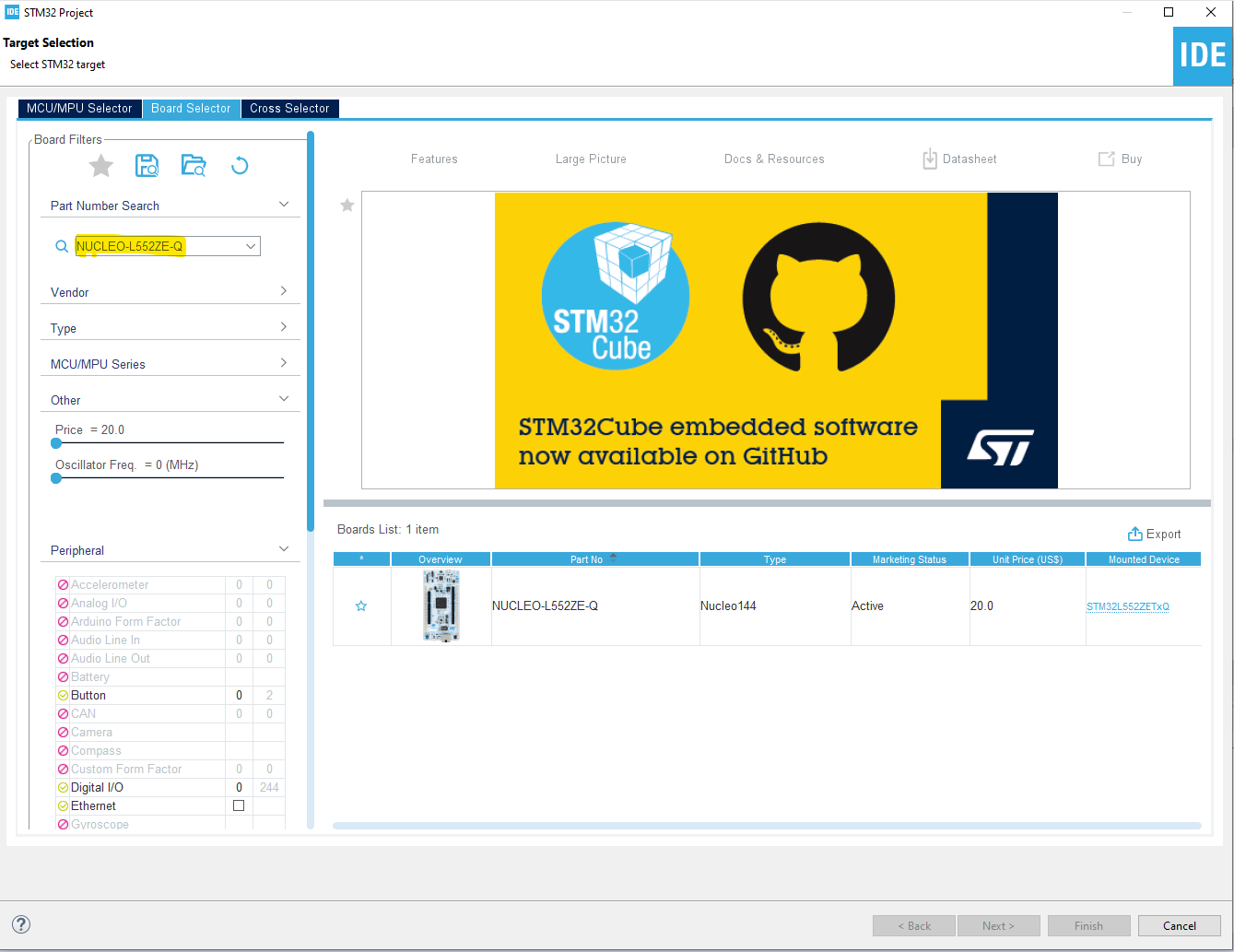
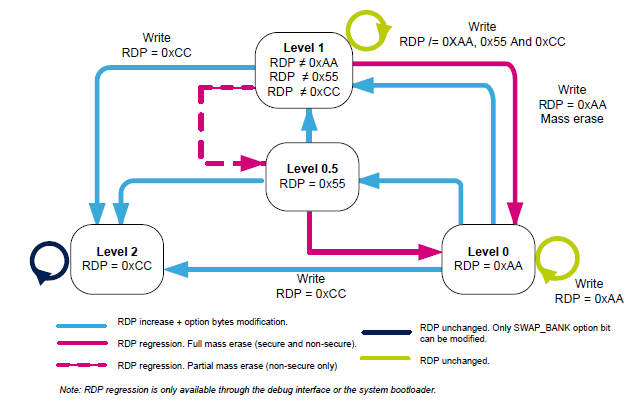
Chapter 10 Vendor: STM32 Embedded Systems Security and TrustZone

Chapter 1 Introduction Embedded Systems Security and TrustZone
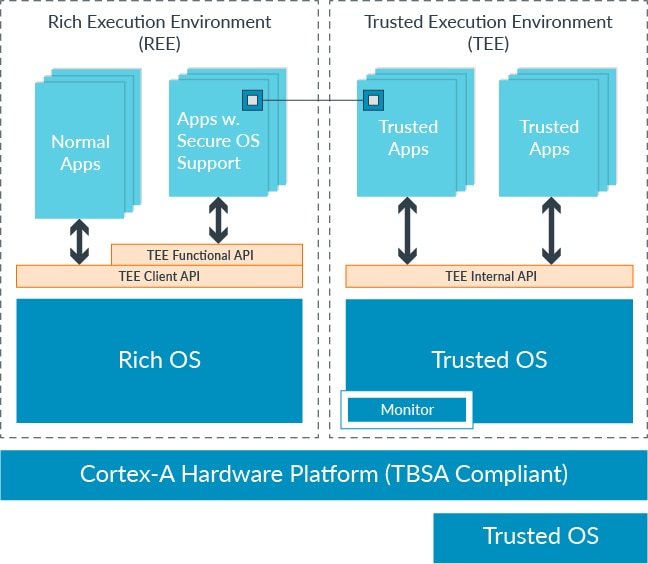
Development of TEE and Secure Monitor Code – Arm®
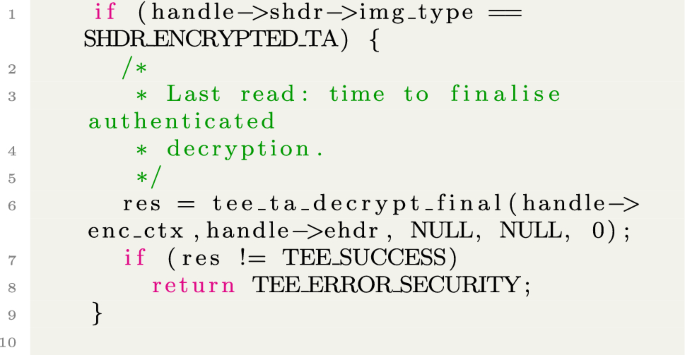
Attacking TrustZone on devices lacking memory protection

Chapter 4 Basics: TrustZone-M Embedded Systems Security and TrustZone
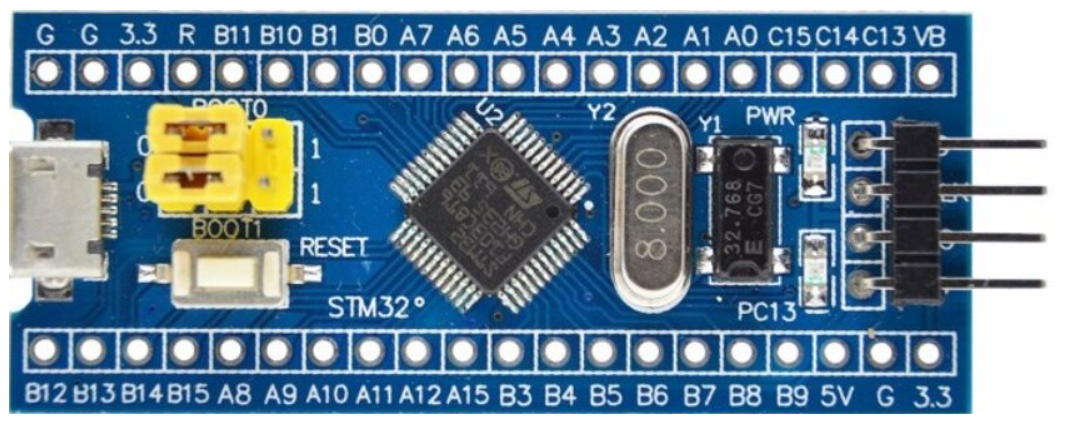
Chapter 10 Vendor: STM32 Embedded Systems Security and TrustZone

Chapter 7 TrustZone-M runtime view (CMSIS Core(M))