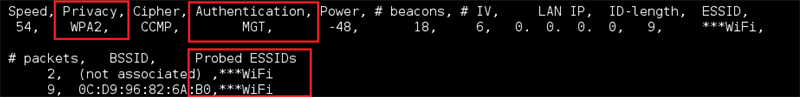
Breaking Down The Critical Security Controls: CSC - 15 Wireless Access Control - Binary Blogger

You network is a collection of wires, wall ports, switches, routers, firewalls and miles of

A guide to CIS Critical Security Controls - Umbrella Managed Systems
Prioritizing a Zero Trust Journey Using CIS Controls v8
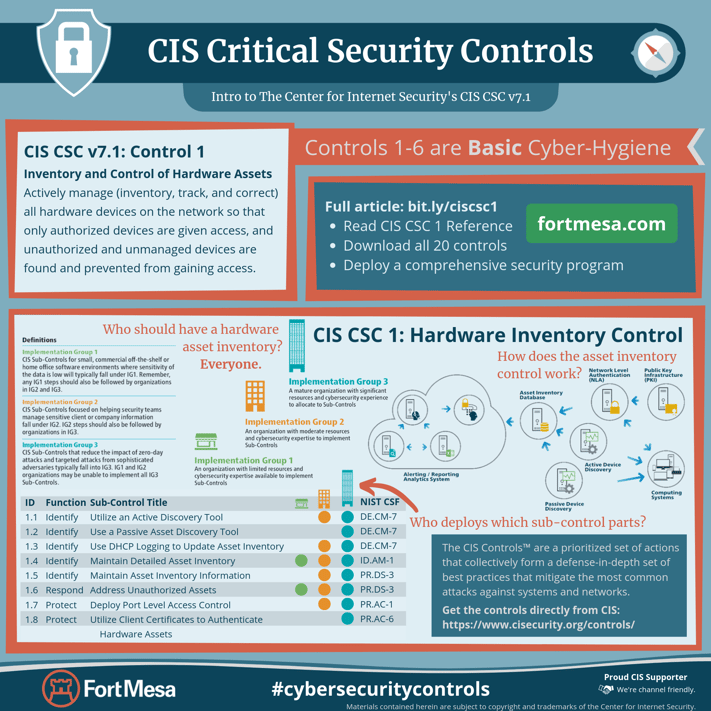
CIS Critical Security Control 1

Understanding the 20 Critical Security Controls: A comprehensive
Top 20 CIS Critical Security Controls (CSC) Through the Eyes of a

CIS controls and how to approach them
Top 20 CIS Critical Security Controls (CSC) Through the Eyes of a

Understanding the 20 Critical Security Controls: A comprehensive

Implementing the CIS Controls to Fight Against the Evolving Threat

How SPOT Monitoring Helps with Top 20 CIS Critical Security

Understanding the 20 Critical Security Controls: A comprehensive

Security risks assessment services — Innovative Penetration








